How to use the mkfs Command on Linux
How to use the stat Command on Linux
How to use Case statements in Bash Scripts
Bash case statements are powerful yet easy to write. When you revisit an old Linux script you’ll be glad you used a case statement instead of a long if-then-else statement.
[mai mult...]How to build a Streaming Radio Server with Icecast on Linux
How to view the System Log on a Mac
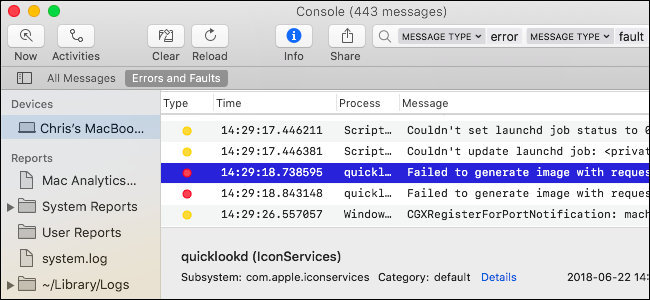
Your Mac keeps system logs, which can help diagnose and troubleshoot problems with macOS and your installed applications. These logs are stored as plain-text log files on your Mac’s system drive, and macOS also includes an app for viewing them.
[mai mult...]DEB Files on Arch? Run Any App on any Linux distro with this tool

Frustrated by an app’s absent or lagging support for your preferred distro? Like magic, Distrobox runs applications from different Linux distributions right on your Linux computer. They’re running on your computer, yet they’re in their own native distribution.
[mai mult...]